Never Do This at Home !!!!!!
CIA
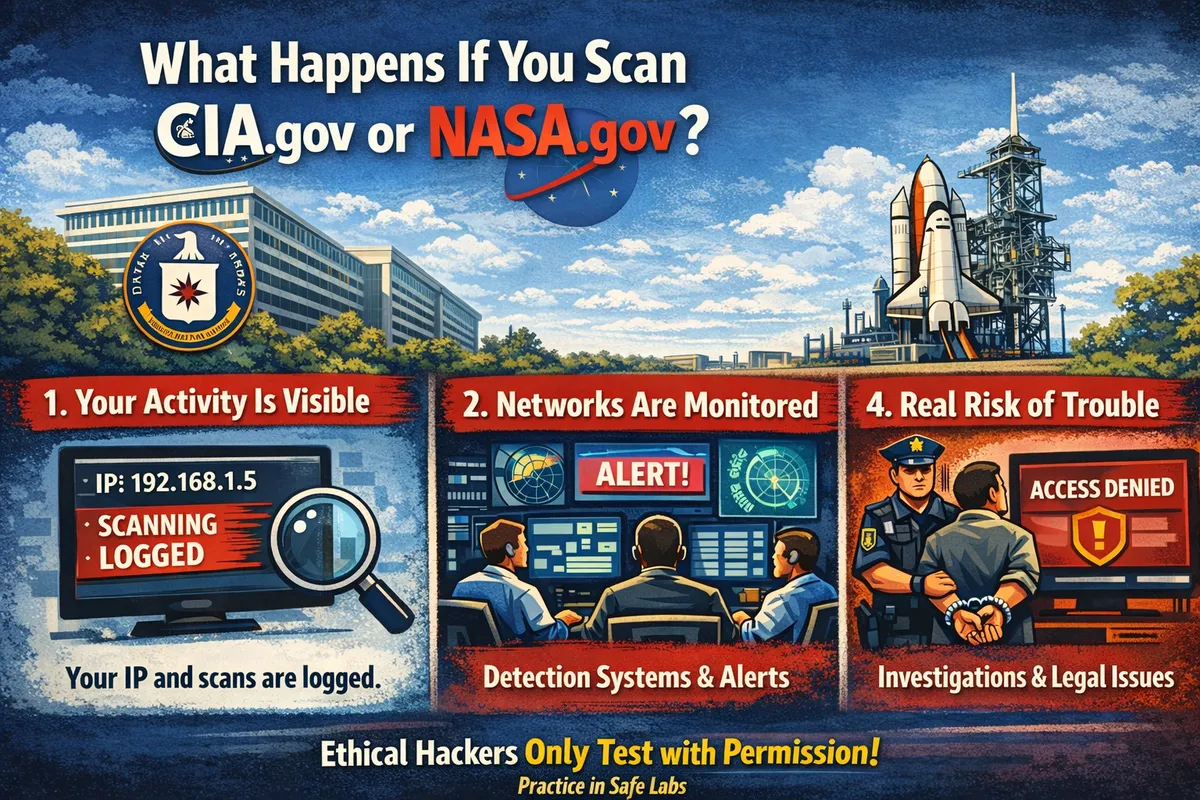
What Happens If Someone Scans CIA.gov or NASA.gov?
Imagine this.
You just learned how to use a scanning tool like Nmap. You open your terminal and type a command.
nmap target.com
Then a thought appears:
“What if I try this on something big… like CIA.gov or NASA.gov?”
For many beginners in cybersecurity, this curiosity happens at some point.
But what would actually happen?
- Your Activity Is Visible
Every request your computer sends to a website includes your IP address and network metadata.
Servers automatically log:
- IP address
- request time
- request type
- traffic pattern
If a scanner suddenly sends many unusual packets, those actions can appear clearly in server logs.
- Government Networks Are Heavily Monitored
Large organizations like government agencies run advanced monitoring systems, including:
- Intrusion Detection Systems (IDS)
- Traffic anomaly detection
- Security monitoring platforms
These systems continuously analyze network traffic and flag unusual behavior like scanning activity.
- Most Likely Outcome
Surprisingly, most of the time:
Nothing dramatic happens.
Large networks receive thousands of automated scans from the internet every single day.
The scan may simply be logged and ignored.
- The Real Risk
The real problem begins if someone tries to go further:
- exploiting vulnerabilities
- brute forcing services
- attempting unauthorized access
At that point, the activity may trigger investigation because government infrastructure is considered a protected system.
Conclusion
Curiosity is normal when learning cybersecurity.
But professionals never test systems without permission.
Ethical hackers practice in safe environments, authorized labs, and legal training platforms instead of scanning random targets on the internet.